Cloud SIEM Audit Logging
The Audit Event Index and System Event Index provide event logs in JSON format on your account activity so you to monitor and audit changes. By default the Audit Event Index and System Event Index are enabled for Cloud SIEM and Enterprise accounts.
This page describes functionality that is available to users whose Cloud SIEM URL ends in sumologic.com.
Where to find documentation
To learn more, see Cloud SIEM audit log definitions.
Scoping your search
This section explains how to scope a search of the Audit Event Index and System Event Index to return Cloud SIEM events.
Limit search to user or system events
Cloud SIEM audit events are stored in two Partitions:
sumologic_audit_events. This index contains user action events, which are events that were triggered by a user action, either from the UI or an API. For example, a user created an insight from a signal using the Cloud SIEM UI.sumologic_system_events. This index contains system action events, which are events that were triggered by the system. For example, an insight was generated by Cloud SIEM.
Use _index=sumologic_audit_events to limit results to events related to user actions
Use _index=sumologic_system_events to limit results to events related to system actions.
Limit search to Cloud SIEM events
You can use the subsystem field, which every event log contains, to limit the events returned to Cloud SIEM-related events:
subsystem=cse*
For information about other fields you can use in Audit Index searches, see auto-generated documentation at the documentation URL for your deployment.
Limit search by Cloud SIEM feature
The table below shows the _sourceCategory that is assigned to event logs by Cloud SIEM feature.
| Product Feature | _sourceCategory Value |
|---|---|
| Action | cseAction |
| Aggregation rule | cseRule |
| Configure assigned insight emails (Relates to the option, on the Actions page, that causes a user to receive an email whenever another user assigns an insight to them.) | cseConfiguration |
| Automation | cseAutomation |
| Chain rule | cseRule |
| Cloud SOAR incident | cseCloudSoar |
| Context action | cseContextAction |
| Custom entity type | cseCustomEntityType |
| Custom insight | cseCustomInsight |
| Custom match list column | cseCustomMatchListColumn |
| Custom tag schema | cseCustomTagSchema |
| Customer sourced entity lookup table | cseCustomerSourcedEntityLookupTable |
| Enrichment | cseEnrichment |
| Entity | cseEntity |
| Entity criticality config | cseEntityCriticalityConfig |
| Entity domain configuration | cseEntityNormalization |
| Entity group configuration | cseEntityGroupConfiguration |
| Entity note | cseEntityNote |
| Favorite field | cseFavoriteField |
| First seen rule | cseRule |
| Insight | cseInsight |
| Insight comment | cseInsightComment |
| Inventory entity lookup table | cseInventoryEntityLookupTable |
| Log mapping | cseLogMapping |
| Match list | cseMatchList |
| Match rule | cseRule |
| MITRE ATT&CK Coverage | cseMitreAttackCoverage |
| Network block | cseNetworkBlock |
| Outlier rule | cseRule |
| Rule Tuning Expression | cseRuleTuningExpression |
| Streaming Export Configuration | cseStreamingExportConfiguration |
| Sumo Logic mapping | cseSumoMapping |
| Suppressed list | cseSuppressList |
| Templated Match Rule | cseRule |
| Threat intel source (Applies to all source types on the Threat Intel page.) | cseThreatIntelSource |
| Threat Intel Source Poll | cseThreatIntelSource |
| Threshold rule | cseRule |
| Virus Total Configuration | cseConfiguration |
| Yara rule | cseYara |
| Yara source | cseYara |
_sourceName and _sourceHost assignment
The _sourceName and _sourceHost fields are assigned to audit event
logs as follows.
| Metadata Field | Assignment Description |
|---|---|
_sourceName | Value of the common parameter, eventName. |
_sourceHost | The remote IP address of the host that made the request. If not available the value will be no_sourceHost. |
Common parameters
Each audit event log has common keys that categorize it to a product area and provide details of the event.
| Parameter | Description | Data Type |
|---|---|---|
accountId | The unique identifier of the organization. | String |
eventId | The unique identifier of the event. | String |
eventName | The name of the event. | String |
eventTime | The event timestamp in ISO 8601 format. | String |
eventFormatVersion | The event log format version. | String |
operator | Information of who did the operation. If it's missing, the Sumo service was the operator. | JSON object of Strings |
subsystem | The product area of the event. | String |
Search for Cloud SIEM events
To search the Audit Event Index or System Event Index for logs that describe Cloud SIEM events:
- Start a log search.
- In the search tab, enter a search using
_indexto specify the partition you want to search, and other metadata or fields to further scope your search. For example:_index=sumologic_system_events
| json auto
| where subsystem="cse*" - Choose the time range for your search.
- Click Start to run the search.
Example event log
Here is an example InsightCreated event log.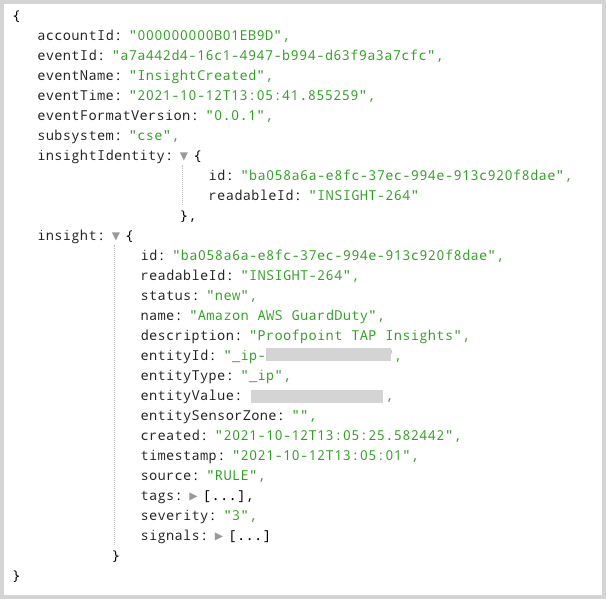
Index retention period
By default, the retention period of the Audit Event Index is the same as the retention period of your Default Partition. You can change the retention period by editing the relevant partitions, sumologic_audit_events and sumologic_system_events. For more information, see Create and Edit a Partition.