Ingest Auth0 Data into Cloud SIEM
To ingest Auth0 data into Cloud SIEM:
- Configure a source for Auth0 on a collector. When you configure the source, do the following:
- Select the Forward to SIEM option in the source configuration UI. This will ensure all logs for this source are forwarded to Cloud SIEM.
- Click the +Add link to add a field whose name is
_parserwith value /Parsers/System/Auth0/Auth0. This ensures that the Auth0 logs are parsed and normalized into structured records in Cloud SIEM.
- Configure Auth0 to send log messages to the Sumo Logic platform. For instructions, see Sumo Logic in the Auth0 help.
- To verify that your logs are successfully making it into Cloud SIEM:
- Classic UI. In the top menu select Configuration, and then under Incoming Data select Log Mappings.
New UI. In the top menu select Configuration, and then under Cloud SIEM Integrations select Log Mappings. You can also click the Go To... menu at the top of the screen and select Log Mappings. - On the Log Mappings tab search for Auth0 and check the Records columns.
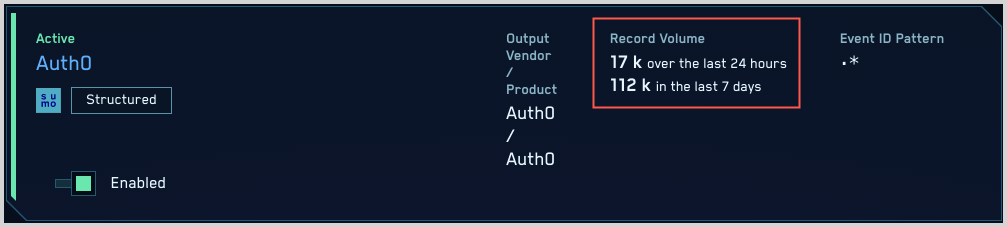
- For a more granular look at the incoming records, you can also use the Sumo Logic platform to search for Auth0 security records:
_index=sec_record* and metadata_product = "Auth0"
- Classic UI. In the top menu select Configuration, and then under Incoming Data select Log Mappings.