Ingest Corelight Zeek Data into Cloud SIEM
To ingest Corelight Zeek data into Cloud SIEM:
- Configure a Syslog source on a collector. When you configure the source, do the following:
- In Source Category, enter a string to tag the output collected from the source. The string that you supply will be saved in a metadata field called
_sourceCategory. Make a note of the source category. You’ll supply it below. - Click the +Add Field link, and add a field whose name is
_siemForwardand value is true. This will ensure all logs for this source are forwarded to Cloud SIEM.
- In Source Category, enter a string to tag the output collected from the source. The string that you supply will be saved in a metadata field called
- Configure a Sumo Logic ingest mapping in Cloud SIEM for the source category assigned to the source you configured above. The mapping tells Cloud SIEM the information it needs to select the right mapper to process messages that have been tagged with that source category.
- New UI. In the main Sumo Logic menu select Cloud SIEM, and then under Cloud SIEM Integrations select Ingest Mappings. You can also click the Go To... menu at the top of the screen and select Ingest Mappings.
Classic UI. In the top Cloud SIEM menu select Configuration, and then and under Integrations select Sumo Logic. - On the Ingest Mappings tab, click + Add Ingest Mapping.
- On the Add Ingest Mapping popup:
- Source Category. Enter the category you assigned to the source above.
- Format. Enter Bro/Zeek JSON.
- Event ID.
{_path}.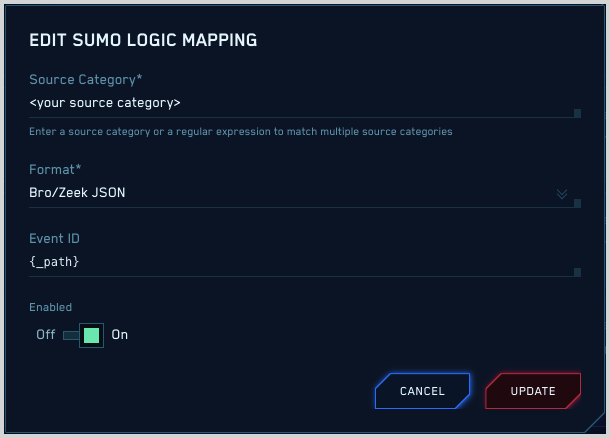
- Click Save to save the mapping.
- New UI. In the main Sumo Logic menu select Cloud SIEM, and then under Cloud SIEM Integrations select Ingest Mappings. You can also click the Go To... menu at the top of the screen and select Ingest Mappings.
- To verify that your logs are successfully making it into Cloud SIEM:
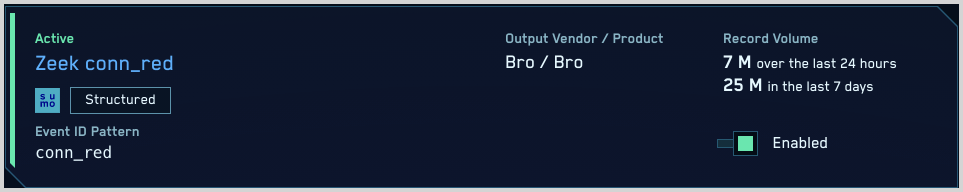
- New UI. In the main Sumo Logic menu select Cloud SIEM, and then under Cloud SIEM Integrations select Log Mappings. You can also click the Go To... menu at the top of the screen and select Log Mappings.
Classic UI. In the top Cloud SIEM menu select Configuration, and then under Incoming Data select Log Mappings. - On the Log Mappings tab search for "Zeek" and check the Records columns.
- For a more granular look at the incoming records, you can also search the Sumo Logic platform for Corelight Zeek security records:
_index=sec_record* and metadata_product = "Zeek"
- New UI. In the main Sumo Logic menu select Cloud SIEM, and then under Cloud SIEM Integrations select Log Mappings. You can also click the Go To... menu at the top of the screen and select Log Mappings.