Integrate Sumo Logic with Google Apps (G Suite) IAM
Availability
| Account Type | Account Level |
|---|---|
| Cloud Flex | Trial, Enterprise |
| Credits | Trial, Essentials, Enterprise Operations, Enterprise Security, Enterprise Suite |
This page has instructions for integrating Sumo Logic SAML with Google Apps IAM. This allows Sumo users to use Google Apps credentials to log into Sumo Logic using Single Sign-On (SSO).
For more information, refer to the Google Support documentation.
Before you start
For key information about SAML in Sumo, see the Limitations section of the "Set Up SAML for Single Sign-On" page.
Configure SSO for a Custom App
-
Log into the Google Admin Console.
-
Select Apps > SAML Apps.
-
Select a new SAML app to be configured, or click the + at the bottom of the page.
-
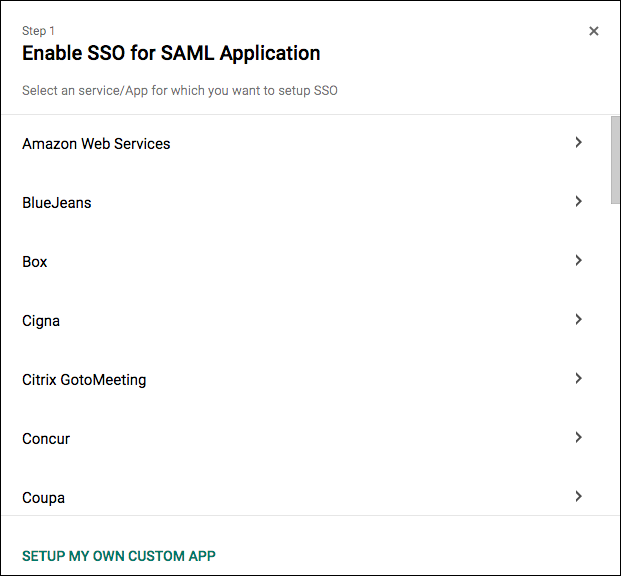
On the Enable SSO for SAML Application page, select Setup my own Custom App at the bottom of the page.
-
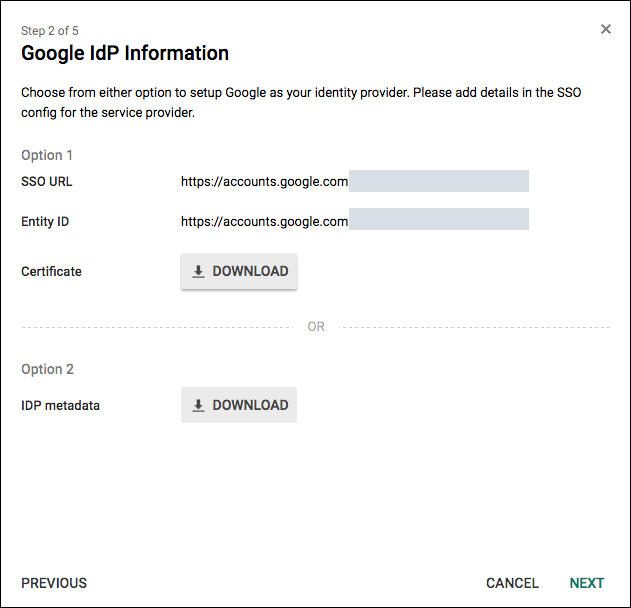
The Google IdP Information page appears. Make note of the following URLs, as you will supply them when you configure SAML in Sumo:
- SSO URL. You'll enter this URL as the Authn Request URL when you perform the steps in Configure Sumo Logic SAML below.
- Entity ID. You'll enter this URL as the Issuer in Sumo Logic when you perform the steps in Configure Sumo Logic SAML below.
-
Click Download for the Certificate.
-
Click Next.
-
In Basic Information for your Custom App page, enter the following:
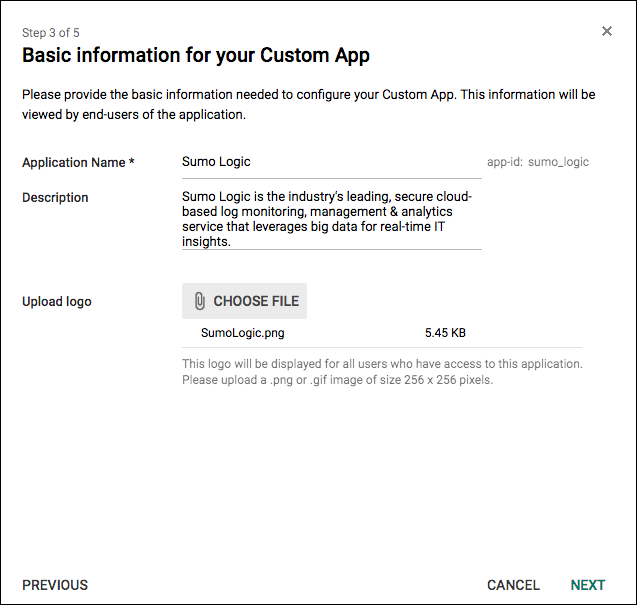
- Application Name. Enter Sumo Logic.
- Description. Sumo Logic is the industry's leading, secure cloud-based log monitoring, management and analytics /img/security that leverages big data for real-time IT insights.
- Upload Logo. Use
sumologic.png.
-
Click Next.
Configure Sumo Logic SAML
- Classic UI. In the main Sumo Logic menu, select Administration > Security > SAML.
New UI. In the top menu select Administration, and then under Account Security Settings select SAML. You can also click the Go To... menu at the top of the screen and select SAML. - Click + Add Configuration to create a new configuration.
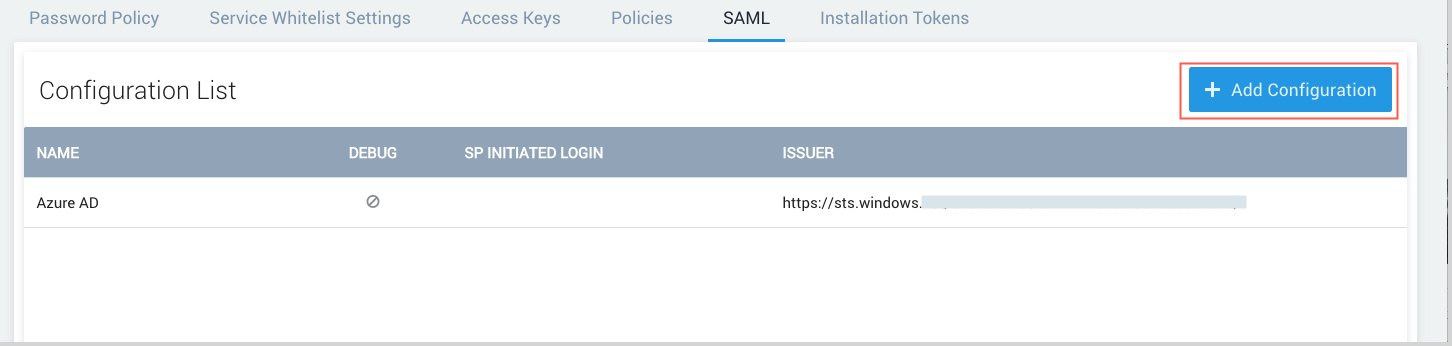
- The Add Configuration page appears.
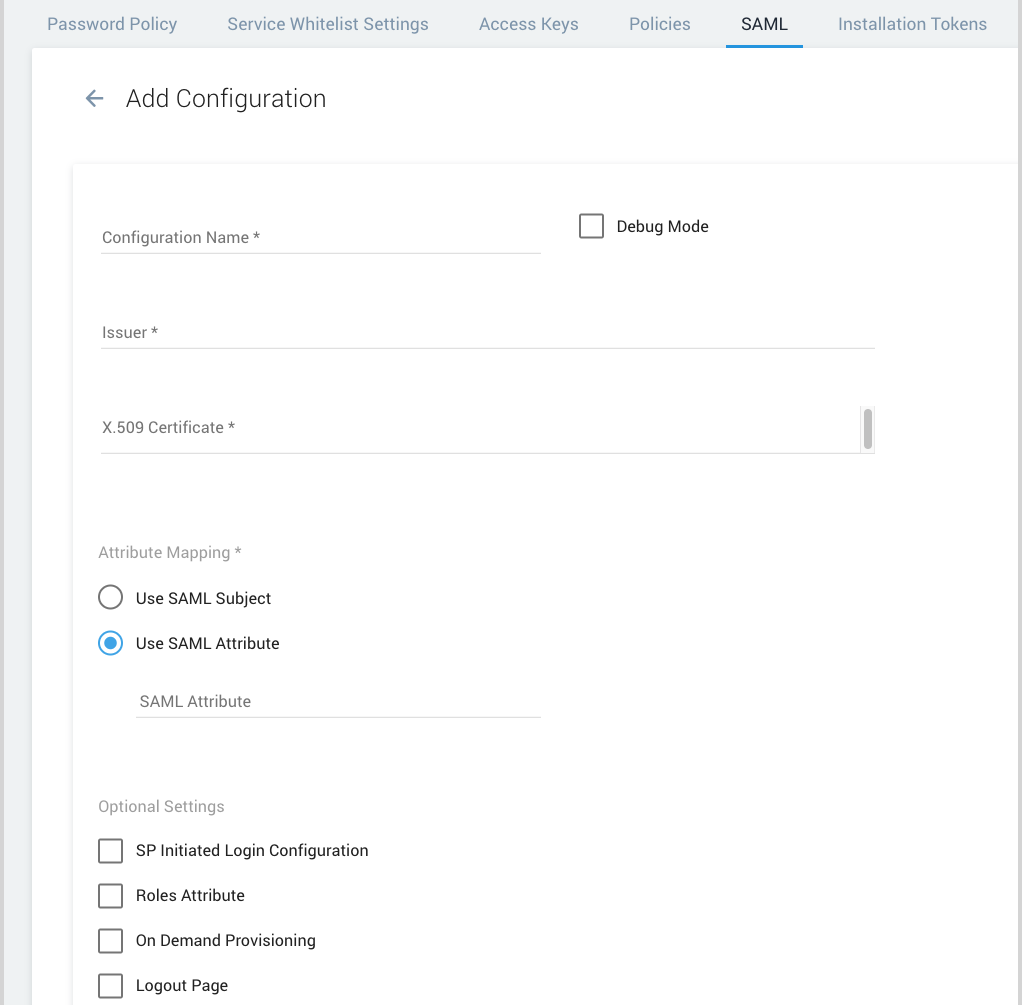
- Configuration Name. Google Apps Auth (or, you can enter any name you like).
- Debug Mode. Not required. Activating this setting now is useful for troubleshooting later. Select this option if you'd like to view additional details if an error occurs when a user attempts to authenticate. For more information, see View SAML Debug Information.
- Issuer. Enter the Entity ID from the Google IdP Information dialog.
- X.509 Certificate. Open the certificate file that you downloaded from the Google IdP Information dialog in a text editor. Copy and paste the contents into this field.
- Attribute Mapping. Select Use SAML attribute and type the email attribute name in the text box.
- SP Initiated Login Configuration. (Optional) This step has instructions for setting up SP-initiated login. When SP initiated login has been enabled, your SAML configuration will appear as an additional authentication option within your subdomain-enabled account login page. SP initiated login requires a custom Sumo Logic subdomain. If a custom subdomain has not yet been configured for your org, following the instructions in the Change account subdomain section of the Manage Organization topic.
- Authn Request URL. Enter the SSO URL from the Google IdP Information dialog.
- Disable Requested Authn Context. (Optional) If you check this option, Sumo will not include the RequestedAuthnContext element of the SAML AuthnRequests it sends to your Idp. This option is useful if your IdP does not support the RequestedAuthnContext element.
- Sign Authn Request. (Optional) If you select this option, Sumo will send signed Authn requests to your IdP. When you click this option, a Sumo-provided X-509 certificate is displayed. You can configure your IDP with this certificate, to verify the signature of the Authn requests sent by Sumo.
- Roles Attribute. When you click this option, the Roles Attribute field appears. Enter the SAML Attribute Name that is sent by the IdP as part of the assertion. For details, see Set Up SAML for Single Sign-On.
- On-Demand provisioning. Select this option and specify the following attributes to have Sumo Logic automatically create accounts when a user first logs on. For more information, see Set Up SAML for Single Sign-On.
- First Name Attribute. FirstName
- Last Name Attribute. LastName
- On Demand Provisioning Roles. Specify the Sumo RBAC roles you want to assign when user accounts are provisioned. (The roles must already exist.)
- Logout Page. Select this option and enter a URL if you'd like to point all users to the URL after logging out of Sumo Logic. For more information, see Set Up SAML for Single Sign-On.
- Click Add to save the configuration.
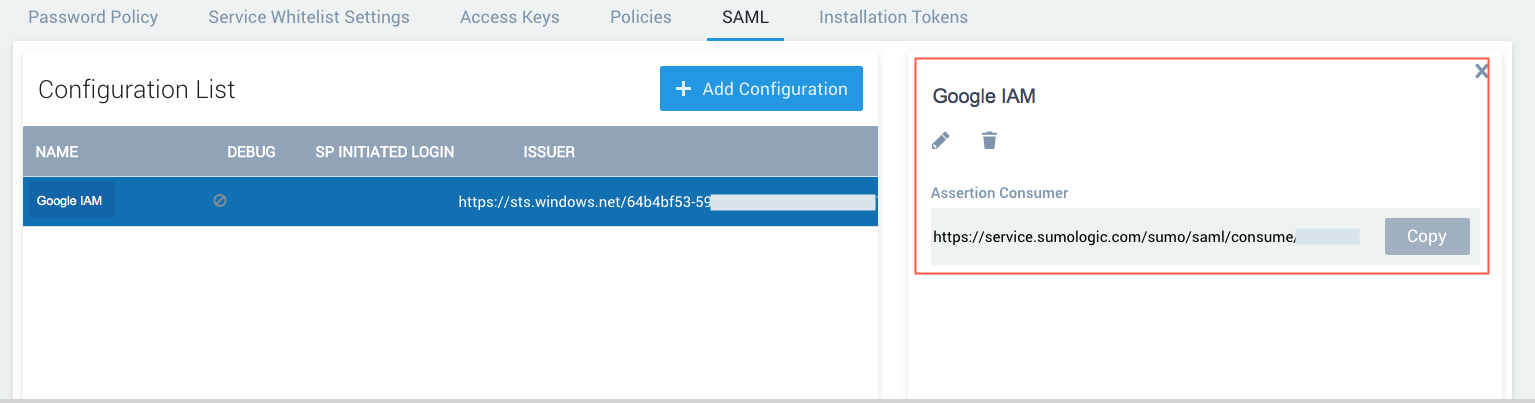
- To view the details of your configuration, select it the Configuration List. The right side of the page displays the Assertion Consumer. You'll need to provide it when you complete the Google SAML configuration.
Complete the Google SAML App Configuration
- Go back to the Google Auth Configuration – Provider Details dialog, and enter the following information:
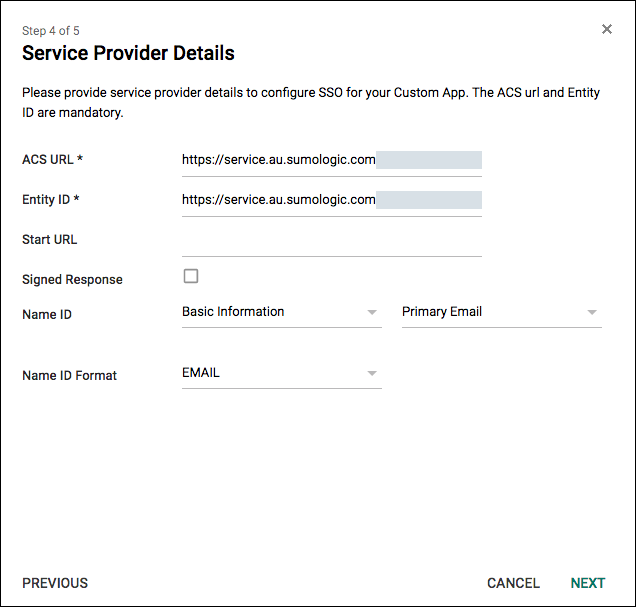
- ACS URL. This is the Assertion Consumer from Sumo Logic
- Entity ID. Enter your Sumo Logic Service Endpoint URL:
https://service.<deployment>.sumologic.com - Name ID. Basic Information – Primary Email
- Name ID Format. EMAIL
- Click Next.
- In the Attribute Mapping dialog, make the following selections:
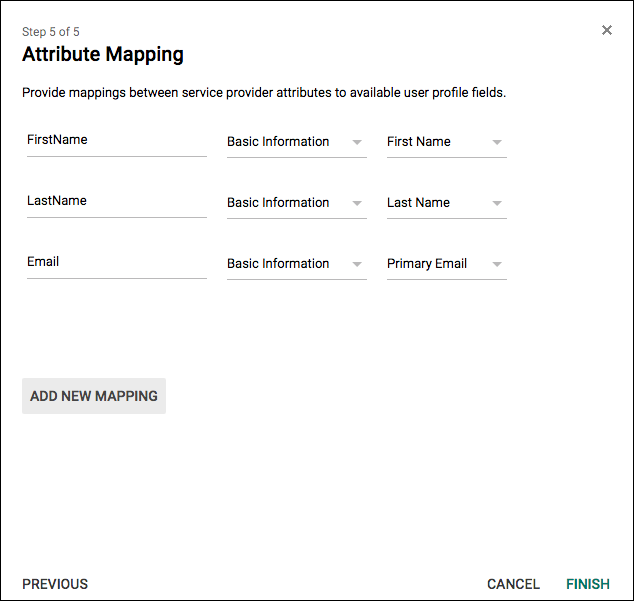
- FirstName. Select Basic Information and First Name.
- LastName. Select Basic Information and Last Name.
- Email. Select Basic Information and Primary Email.
- Click Finish.
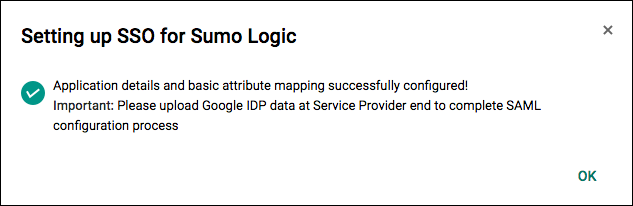
- The Settings for Sumo Logic page is displayed, and you should see the success message Setting up SSO for Sumo Logic. Click OK.
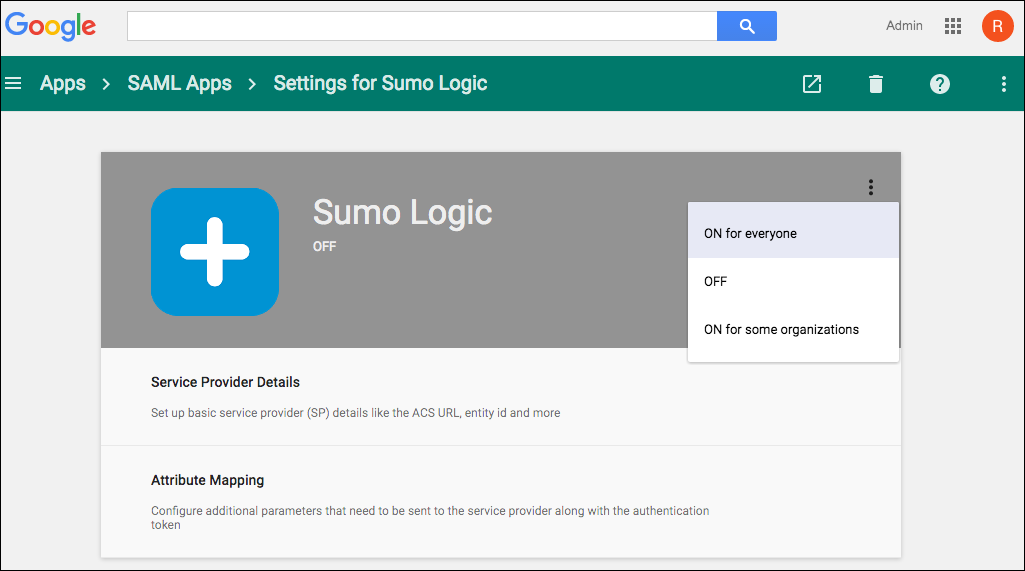
- To enable the Sumo Logic App for everyone, from the menu, select On for everyone.
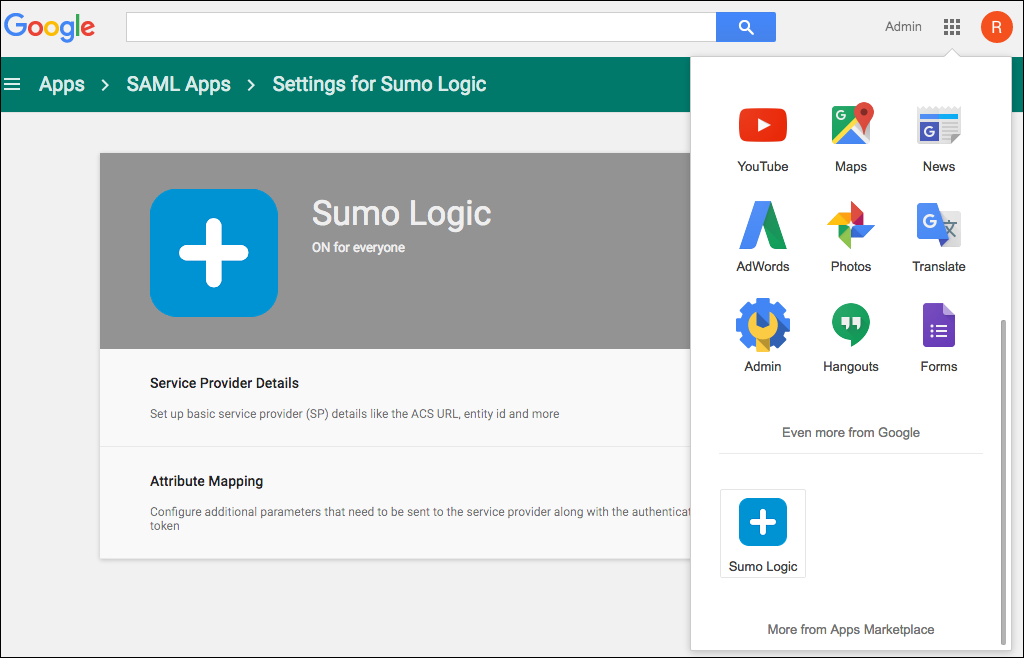
- After a short delay, the new Sumo Logic SAML App will be displayed in your Google Apps login menu. In some cases, it may take up to 10 minutes for the new app to appear.
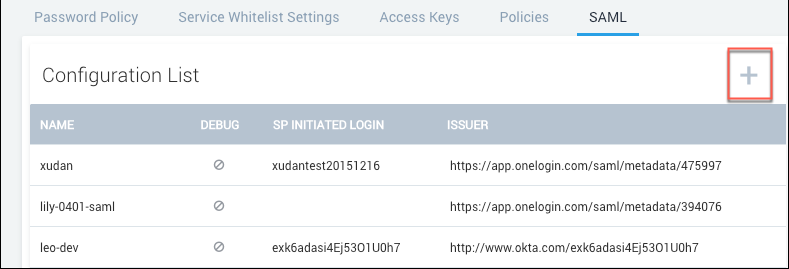
Create multiple SAML configurations
You can create multiple SAML configurations in Sumo. To create an additional SAML configuration, click the plus (+) icon to create a new configuration. Enter the settings for the new configuration, as described the previous section.
Require SAML for sign-in
After you create a SAML configuration, you can require users to sign in using SAML and prevent users from bypassing SAML with a username and password for login. Before you do so, follow the instructions in Check SAML Usage.
Check SAML Usage
If you intend to require Sumo users to sign-in using SAML, as described in the following section, Require SAML for sign-in, it is a best practice to first check whether some users are still logging in directly, instead of using SAML. You can run the following query to see, for a particular time range, whether users signed in using SAML or with their username and password:
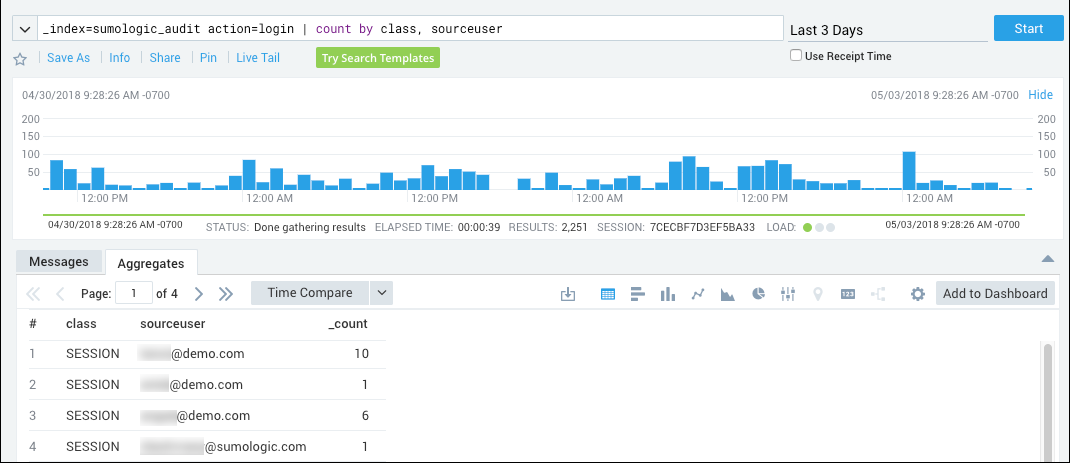
_index=sumologic_audit action=login | count by class, sourceuser
This query depends upon data in the Sumo audit index. If the audit index is not enabled, the query will not return results. To enable the index, follow the instructions in Enable and Manage the Audit Index.
The query results show, for each user that has accessed Sumo over the time range, the number of times they have logged in using SAML or by entering a Sumo username and password. In the class column:
- "SAML" indicates the user signed in using SAML.
- "SESSION" indicates the user authenticated by entering a username and password.
If the same user accessed Sumo using both methods (SAML and direct logon) during the time range, the query results will include a row for each method, showing how many times each method was used.
Require SAML for sign-in
Click Require SAML Sign In to require users to sign in using SAML.
After you lock down SAML, any new users you allowlist will have to select Forgot Password from the login screen to recover their credentials. This is because a SAML-locked down user does NOT have a password.
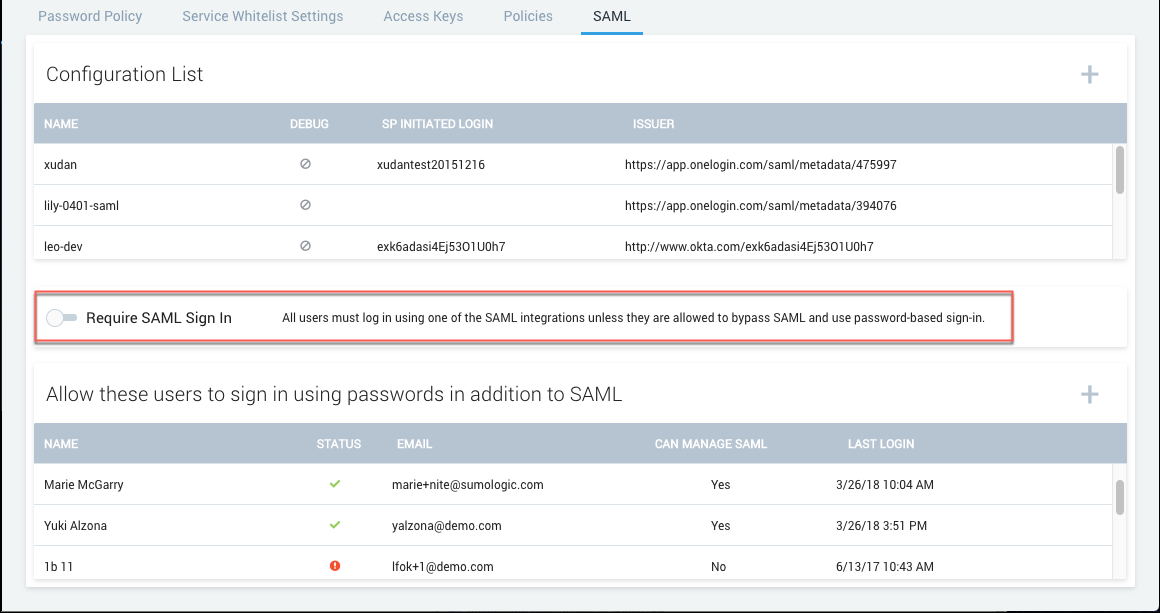
Sumo automatically adds your account under Allow these users to sign in using passwords in addition to SAML as an allowlisted user as a preventative measure to ensure you’re still able to access Sumo if you run into issues.
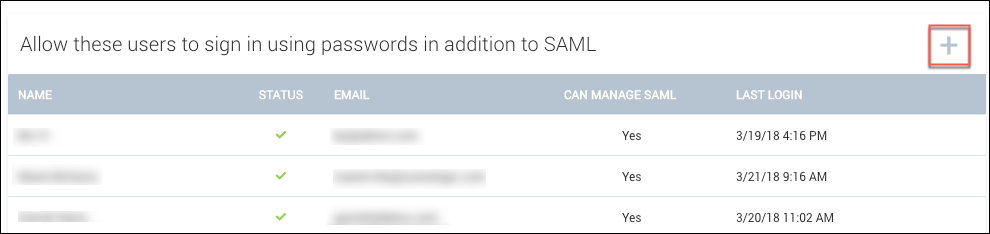
Having only one user able to bypass SAML may not be convenient or practical if you have a global company or a large team. You can add additional allowlisted users by clicking the (+) icon next to Allow these users to sign in using passwords in addition to SAML:
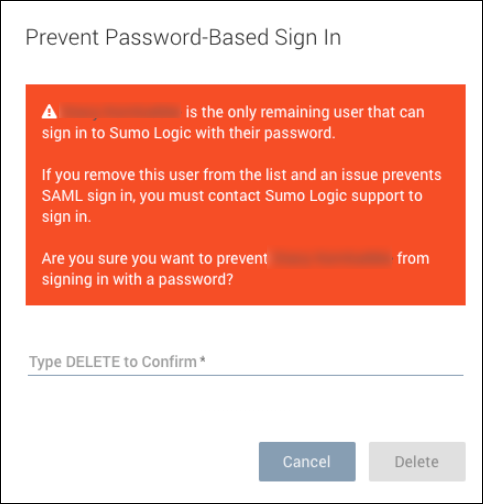
We do not recommend denying all users password access to Sumo even if you want to enforce log in by SAML. If you attempt to delete your last remaining allowlisted user, you will receive a warning that this is not a recommended practice:
SAML lockdown limitations
There are user account changes an admin cannot perform when the Require SAML Sign In option is selected:
- You cannot change a user's login email address when SAML is locked down.
- You cannot reset a user's password when SAML is locked down.
- If a user's account has been locked as a result of too many failed login attempts, you cannot unlock the account while SAML is locked down.
To make these changes, you must toggle off the Require SAML Sign In option, make the updates, and then turn Require SAML Sign In back on.