Kaspersky TIP

Version: 1.1
Updated: Jul 05, 2023
Quickly determine whether an investigated object is dangerous or clean by requesting detailed information about URLs, IP addresses and hashes from the Kaspersky Threat Intelligence Portal, directly from Sumo Logic SOAR Platform.
Actions
- Search Intelligence (Enrichment) - Search for incident indicators from Kaspersky threat intelligence feeds.
Configure Kaspersky TIP in Automation Service and Cloud SOAR
Before you can use this automation integration, you must configure its authentication settings so that the product you're integrating with can communicate with Sumo Logic. For general guidance, see Configure Authentication for Automation Integrations.
How to open the integration's configuration dialog
- Access App Central and install the integration. (You can configure at installation, or after installation with the following steps.)
- Go to the Integrations page.
Classic UI. In the main Sumo Logic menu, select Automation and then select Integrations in the left nav bar.
New UI. In the main Sumo Logic menu, select Automation > Integrations. You can also click the Go To... menu at the top of the screen and select Integrations. - Select the installed integration.
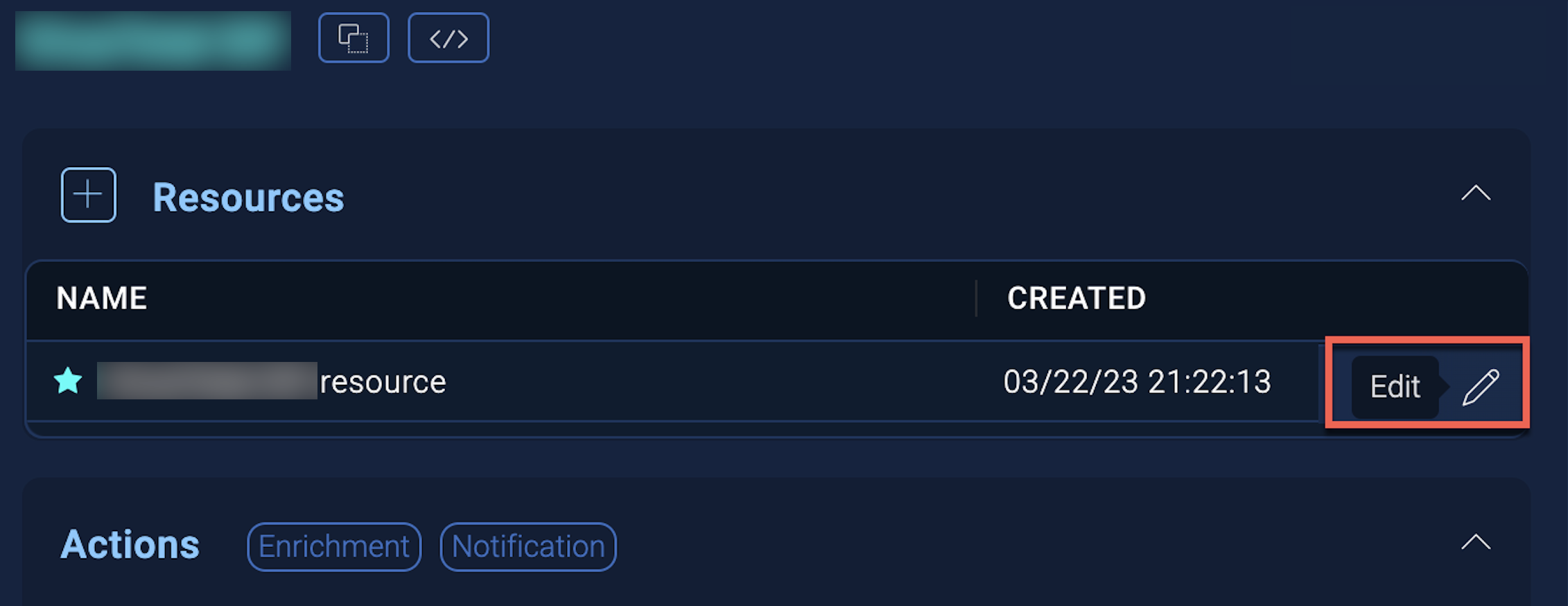
- Hover over the resource name and click the Edit button that appears.
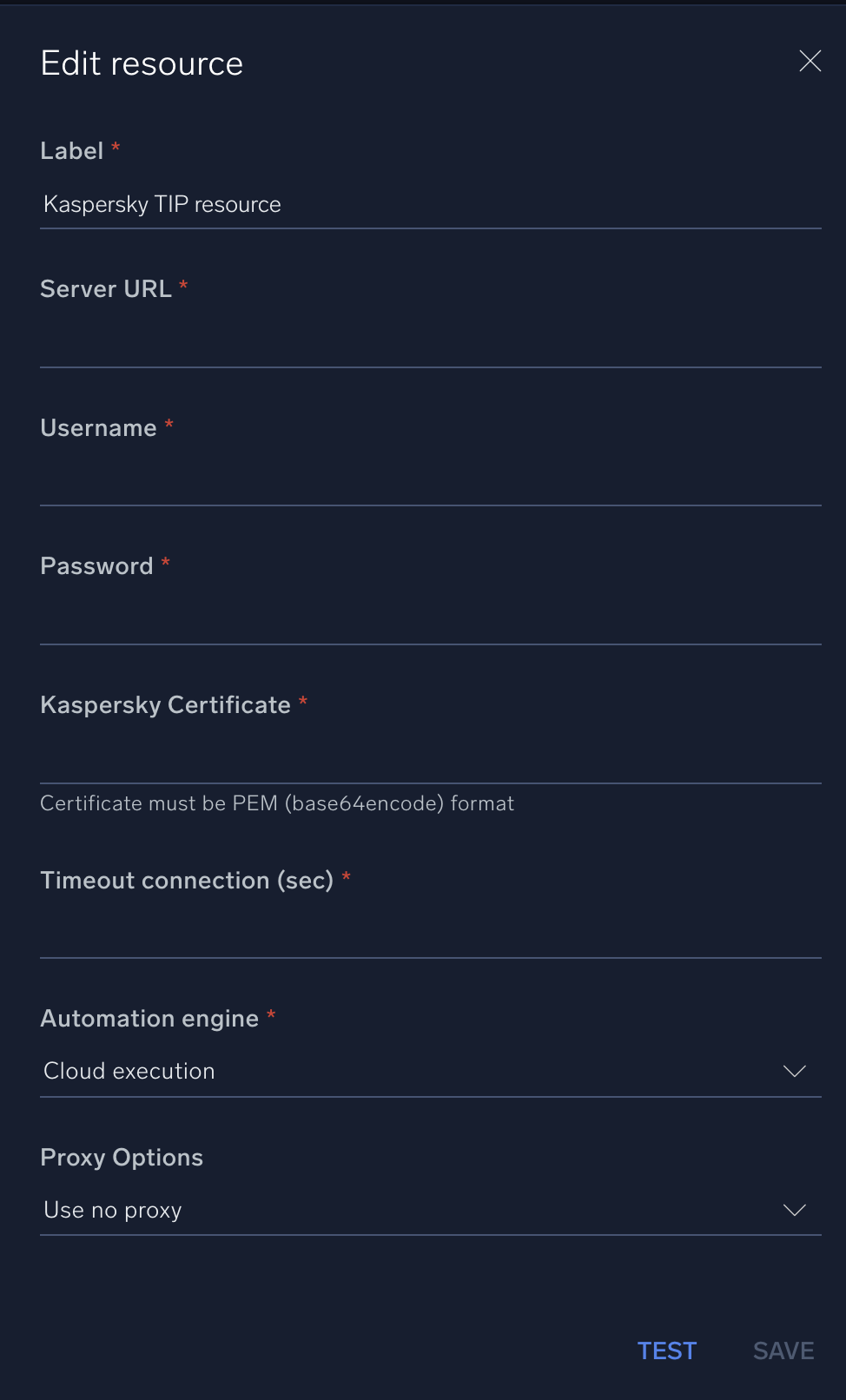
In the configuration dialog, enter information from the product you're integrating with. When done, click TEST to test the configuration, and click SAVE to save the configuration:
-
Label. Enter the name you want to use for the resource.
-
Server URL. Enter your Kaspersky TIP server URL.
-
Username. Enter the username of a Kaspersky TIP admin user authorized to provide authentication for the integration.
-
Password. Enter the password for the admin user.
-
Kaspersky Certificate. Enter the Kaspersky certificate. The certificate must be in PEM (base64encode) format.
-
Connection Timeout (s). Set the maximum amount of time the integration will wait for a server's response before terminating the connection. Enter the connection timeout time in seconds (for example,
180). -
Automation Engine. Select Cloud execution for this certified integration. Select a bridge option only for a custom integration. See Cloud or Bridge execution.
-
Proxy Options. Select whether to use a proxy. (Applies only if the automation engine uses a bridge instead of cloud execution.)
- Use no proxy. Communication runs on the bridge and does not use a proxy.
- Use default proxy. Use the default proxy for the bridge set up as described in Using a proxy.
- Use different proxy. Use your own proxy service. Provide the proxy URL and port number.
For information about Kaspersky TIP, see Kaspersky TIP documentation.
Change Log
- July 10, 2019 - First upload
- January 22, 2020 - Updated "search Intelligence" action
- July 5, 2023 (v1.1) - Updated the integration with Environmental Variables