Symantec Web Security Service Source

The Symantec Web Security Service Source provides a secure endpoint to receive WSS Access logs from the Symantec WSS API. It securely stores the required authentication, scheduling, and state tracking information.
- See the Access Log Format for reference.
- Logs are ingested in batches of 1,000.
- Logs are polled every five minutes.
Data collected
| Polling Interval | Data |
|---|---|
| 5 min | WSS Access logs |
Setup
Vendor configuration
You need to configure a WSS agent on the machine you want to collect data from. The WSS agent will collect your access data and the Symantec Web Security Service Source will receive that data using the Symantec WSS API. To configure and install the agent, follow the instructions in the Web Security Service documentation.
You need to have a Symantec Web Security Service username and password. To create a User API Key that serves as the username and password in the Sync API syntax follow these steps:
- Navigate to Account Configuration > API Credentials.
- Click Add API Credentials.
- WSS displays the Add API Credential dialog, which contains the random characters Username and Password.
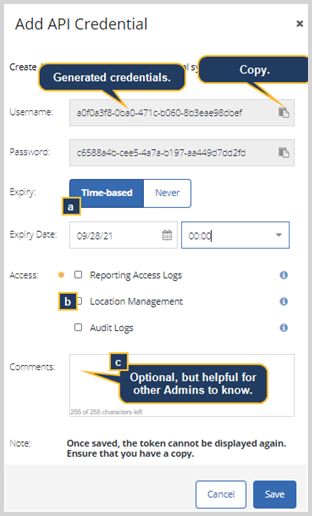
- Copy the Username and Password keys into a text file.
- Select the API Expiry you'd like to set.
- Time-based—You define the date and time when this token expires.
- Never expires.
- For the Access option, select Reporting Access Logs.
- Click Save.
See Symantec Security Software documentation for further details on generating API credentials.
Source configuration
When you create a Symantec Web Security Service Source, you add it to a Hosted Collector. Before creating the Source, identify the Hosted Collector you want to use or create a new Hosted Collector. For instructions, see Configure a Hosted Collector.
To configure a Symantec Web Security Service Source:
- New UI. In the Sumo Logic main menu select Data Management, and then under Data Collection select Collection. You can also click the Go To... menu at the top of the screen and select Collection.
Classic UI. In the main Sumo Logic menu, select Manage Data > Collection > Collection. - On the Collectors page, click Add Source next to a Hosted Collector.
- Select Symantec Web Security Service.
- Enter a Name to display for the Source in the Sumo web application. The description is optional.
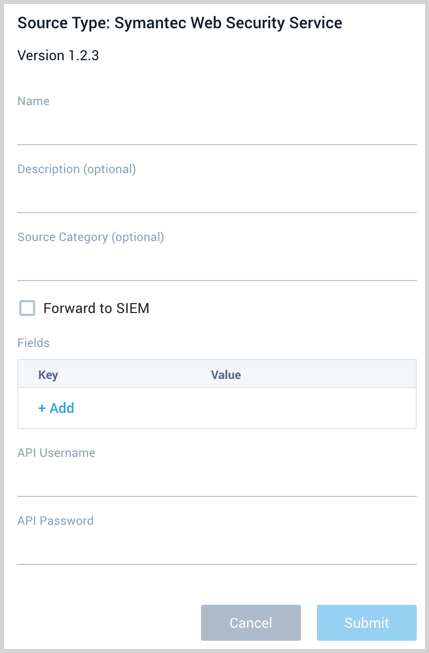
- (Optional) For Source Category, enter any string to tag the output collected from the Source. Category metadata is stored in a searchable field called
_sourceCategory. - Forward to SIEM. Check the checkbox to forward your data to Cloud SIEM. note
Select Forward to SIEM only if you have Cloud SIEM installed.
- (Optional) Fields. Click the +Add Field link to define the fields you want to associate, each field needs a name (key) and value.
 A green circle with a check mark is shown when the field exists and is enabled in the Fields table schema.
A green circle with a check mark is shown when the field exists and is enabled in the Fields table schema. An orange triangle with an exclamation point is shown when the field doesn't exist in the Fields table schema. In this case, you'll see an option to automatically add or enable the nonexistent fields to the Fields table schema. If a field is sent to Sumo Logic but isn’t present or enabled in the schema, it’s ignored and marked as Dropped.
An orange triangle with an exclamation point is shown when the field doesn't exist in the Fields table schema. In this case, you'll see an option to automatically add or enable the nonexistent fields to the Fields table schema. If a field is sent to Sumo Logic but isn’t present or enabled in the schema, it’s ignored and marked as Dropped.
- API Username and Password. Provide the Symantec Web Security Service user credentials you want to use to authenticate collection requests. This was copied during the Vendor configuration steps above.
- When you are finished configuring the Source, click Submit.
Metadata fields
| Field | Value | Description |
|---|---|---|
_siemVendor | Symantec | Set when Forward To SIEM is checked. |
_siemProduct | Web Security Service | Set when Forward To SIEM is checked. |
_siemFormat | JSON | Set when Forward To SIEM is checked. |
_siemEventID | proxy-messages | Set when Forward To SIEM is checked and specific to the API collected. |
JSON schema
Sources can be configured using UTF-8 encoded JSON files with the Collector Management API. See how to use JSON to configure Sources for details.
| Parameter | Type | Value | Required | Description |
|---|---|---|---|---|
| schemaRef | JSON Object | {"type":"Symantec Web Security Service"} | Yes | Define the specific schema type. |
| sourceType | String | "Universal" | Yes | Type of source. |
| config | JSON Object | Configuration object | Yes | Source type specific values. |
Configuration Object
| Parameter | Type | Required | Default | Description | Example |
|---|---|---|---|---|---|
| name | String | Yes | null | Type a desired name of the source. The name must be unique per Collector. This value is assigned to the metadata field _source. | "mySource" |
| description | String | No | null | Type a description of the source. | "Testing source" |
| category | String | No | null | Type a category of the source. This value is assigned to the metadata field _sourceCategory. See best practices for details. | "mySource/test" |
| fields | JSON Object | No | null | JSON map of key-value fields (metadata) to apply to the Collector or Source. Use the boolean field _siemForward to enable forwarding to SIEM. | {"_siemForward": false, "fieldA": "valueA"} |
| apiUsername | String | Yes | null | Provide the username you want to use to authenticate collection requests. | |
| apiPassword | String | Yes | null | Provide the password for the username that you want to use to authenticate collection requests. |
JSON example
loading...
Terraform example
loading...
FAQ
Click here for more information about Cloud-to-Cloud sources.