Microsoft Azure Activity Log - Cloud SIEM
This section has instructions for collecting Azure Activity log messages and sending them to Sumo Logic to be ingested by Cloud SIEM.
Step 1: Configure collection
In this step, you configure an HTTP Source to collect Azure Activity log messages. You can configure the source on an existing Hosted Collector or create a new collector. If you’re going to use an existing collector, jump to Configure an HTTP Source below. Otherwise, create a new collector as described in Configure a hosted collector below, and then create the HTTP Source on the collector.
Configure a Hosted Collector
- Classic UI. In the main Sumo Logic menu, select Manage Data > Collection > Collection.
New UI. In the top menu select Configuration, and then under Data Collection select Collection. You can also click the Go To... menu at the top of the screen and select Collection. - Click Add Collector.
- Click Hosted Collector.
- The Add Hosted Collector popup appears.
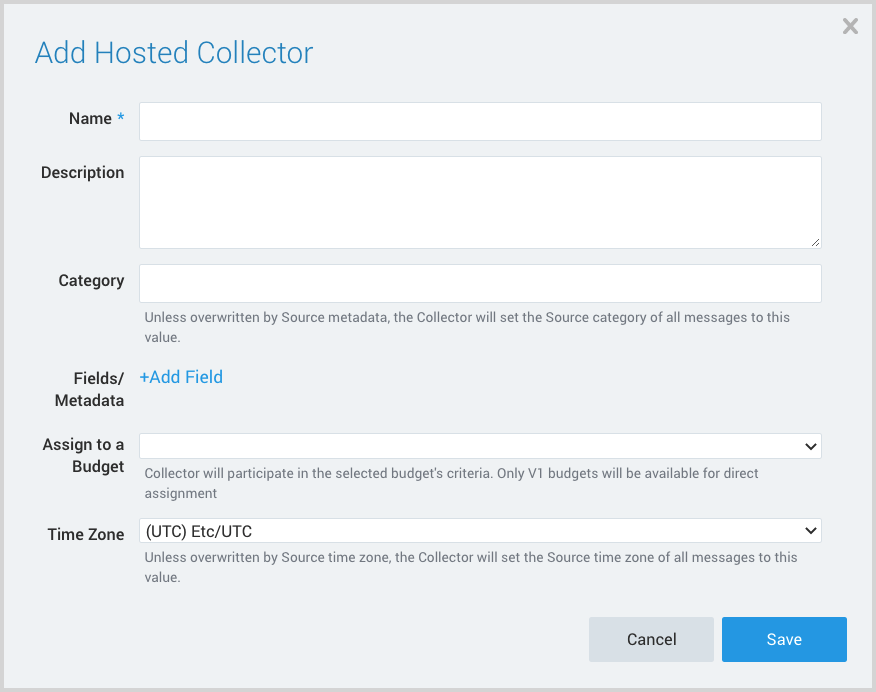
- Name. Provide a Name for the Collector.
- Description. (Optional)
- Category. Enter a string to tag the output collected from the source. The string that you supply will be saved in a metadata field called
_sourceCategory. - Fields.
- If you are planning that all the sources you add to this collector will forward log messages to Cloud SIEM, click the +Add Field link, and add a field whose name is
_siemForwardand value is true. This will cause the collector to forward all of the logs collected by all of the sources on the collector to Cloud SIEM. - If all sources in this collector will be Microsoft Azure sources, add an additional field with key
_parserand value /Parsers/System/Microsoft/Microsoft Azure JSON.
noteIt’s also possible to configure individual sources to forward to Cloud SIEM, as described in the following section.
- If you are planning that all the sources you add to this collector will forward log messages to Cloud SIEM, click the +Add Field link, and add a field whose name is
Configure an HTTP Source
- Classic UI. In the main Sumo Logic menu, select Manage Data > Collection > Collection.
New UI. In the top menu select Configuration, and then under Data Collection select Collection. You can also click the Go To... menu at the top of the screen and select Collection. - Navigate to the Hosted Collector where you want to create the source.
- On the Collectors page, click Add Source next to a Hosted Collector.
- Select HTTP Logs & Metrics.
- The page refreshes.
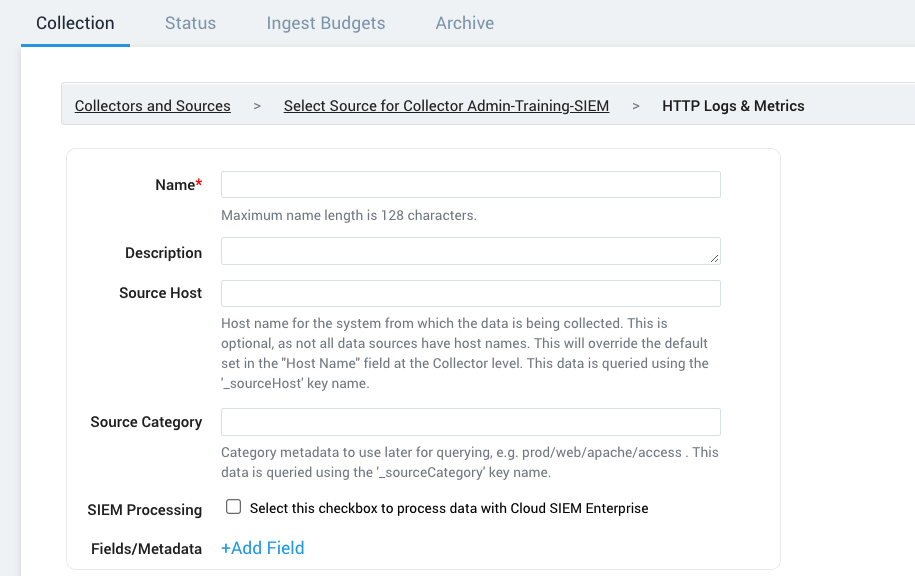
- Name. Enter a name for the source.
- Description. (Optional)
- Source Host. (Optional) Enter a string to tag the messages collected from the source. The string that you supply will be saved in a metadata field called
_sourceHost. - Source Category. Enter a string to tag the output collected from the source. The string that you supply will be saved in a metadata field called
_sourceCategory. - Fields. If you are not parsing all sources in the hosted collector with the same parser, click the +Add Field link, and add a field whose name is
_parserwith value /Parsers/System/Microsoft/Microsoft Azure JSON. - Advanced Options for Logs. For information about the optional advance options you can configure, see HTTP Logs and Metrics Source.
- Click Save.
- Make a note of the HTTP Source URL that is displayed. You’ll supply it in Step 2 below.
Step 2: Configure Azure Activity Log
In this step you configure Azure Activity Log to send log messages to the Sumo Logic platform. For instructions, see steps for Collecting Logs for the Azure Audit App from Event Hub.
Step 3: Verify ingestion
In this step, you verify that your logs are successfully making it into Cloud SIEM.
- Classic UI. In the top menu select Configuration, and then under Incoming Data select Log Mappings.
New UI. In the top menu select Configuration, and then under Cloud SIEM Integrations select Log Mappings. You can also click the Go To... menu at the top of the screen and select Log Mappings. - On the Log Mappings tab search for "Azure" and check the Records columns.
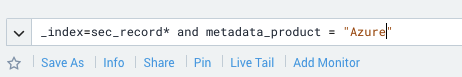
- For a more granular look at the incoming records, you can also search the Sumo Logic platform for Azure security records.